By A Mystery Man Writer

Learn how to secure your Elastic Stack deployment for free using capabilities such as TLS encryption, role-based access control, and multi-tenancy features to support your organization’s needs. Elasticsearch and Kibana product management leaders will outline how to approach Elastic Stack security from a holistic perspective and share guidance as well as lessons learned.

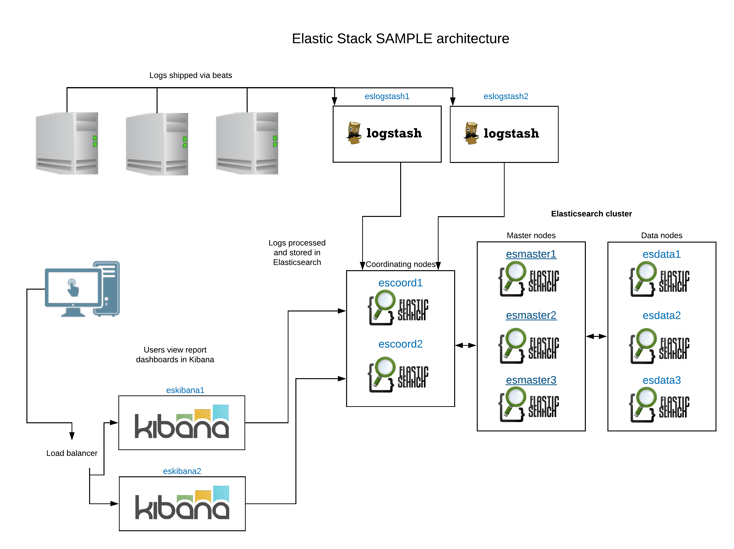
What Is Elasticsearch, Logstash, and Kibana? A Detailed Guide

5 steps for securing your Elasticsearch cluster

Elastic SIEM: Speed, scale, and analytical power drive your security operations and threat hunting - Help Net Security

Mappy hour: Uncovering insights with Elastic Maps and location data

API Key Implementation On ELK Stack, by Johanesmistrialdo
/hs-fs/hubfs/Imported_Blog_Media/Sa

Aris Papadopoulos on LinkedIn: We are continuously evolving the core Elastic stack capabilities that…

Automating the Elastic Stack
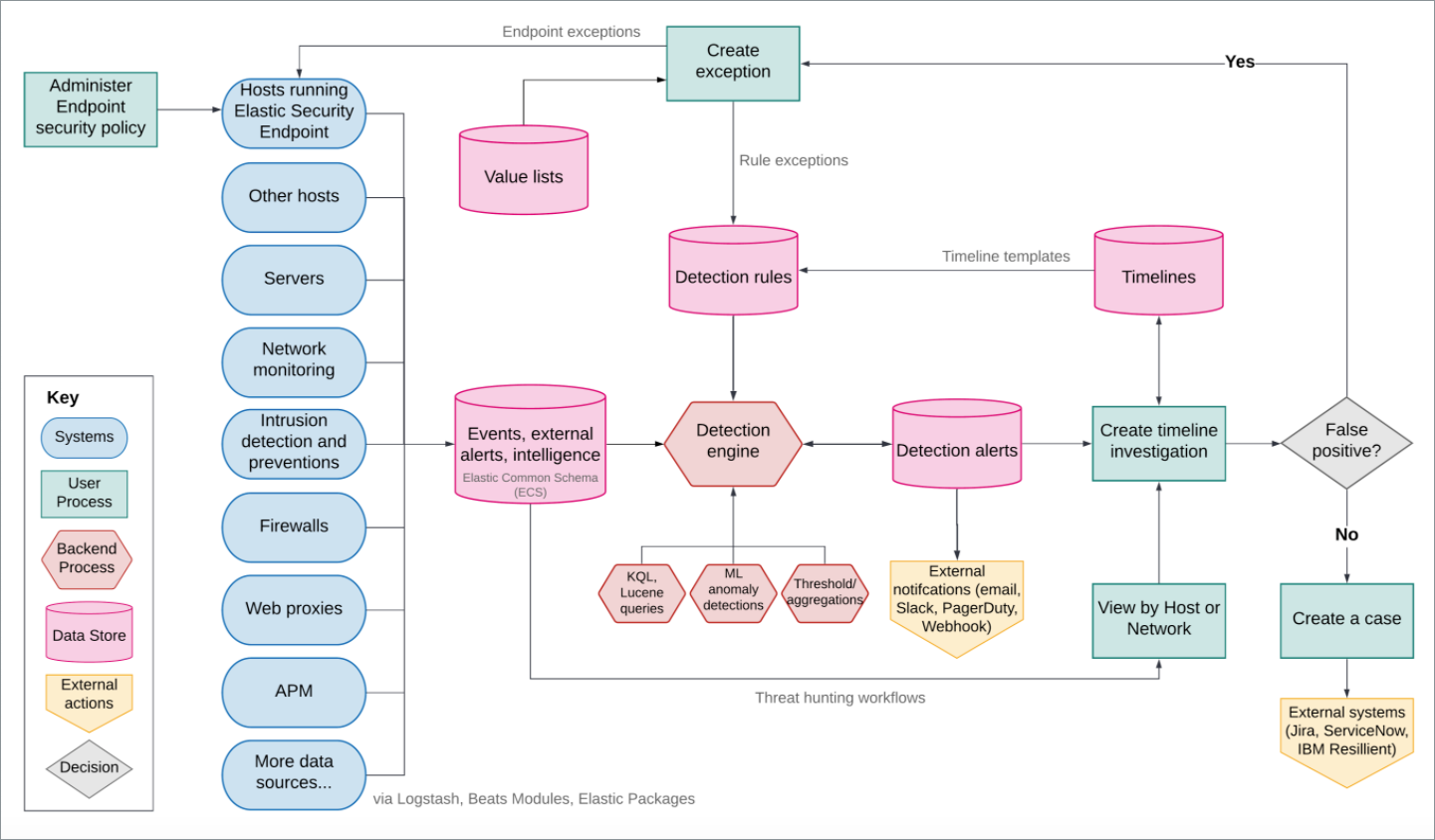
Elastic Security overview, Elastic Security Solution [7.17]

Free authentication integration of Kibana with OIDC and LDAP using Keykloak, Apache Reverse Proxy, and X-PACK enabled, by Hamza Mourad

ELK Stack : Get Started with Elasticsearch, Logstash, Kibana, & Beats

Aris Papadopoulos on LinkedIn: We are continuously evolving the core Elastic stack capabilities that…
How to Install ELK Stack on CentOS 8